SECURELYTIX BLOG
Security Insights
Practical guides on AI security, data protection, encryption, compliance, and privacy-first infrastructure.
Raw PII: The Most Dangerous Technical Debt in Modern Systems
Read the full post.
Why the Frontend Is One of the Most Dangerous Places for PII And How to Fix It Architecturally
Modern frontend applications handle sensitive user data across APIs, browser storage, analytics tools, and third-party scripts making the browser one of the largest yet least protected PII exposure surfaces. This article explores why frontend architectures leak sensitive data and how privacy-first design patterns like tokenization and secure data flow isolation help reduce risk.
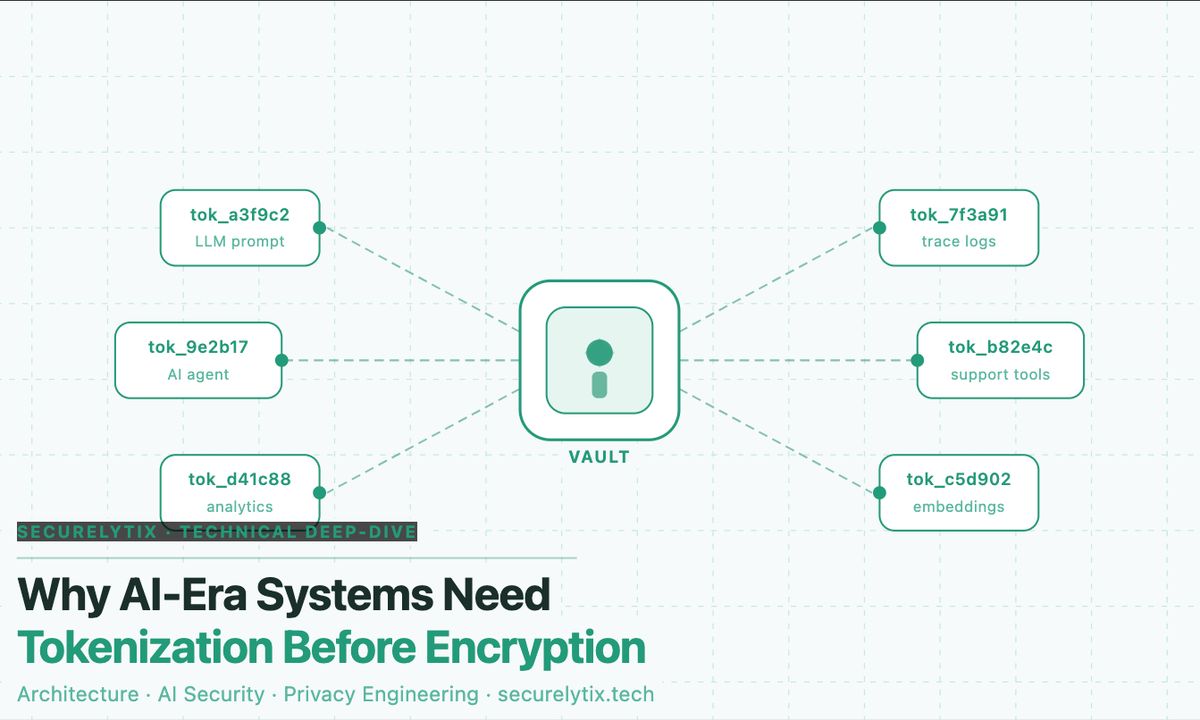
Why AI-Era Systems Need Tokenization Before Encryption
By Securelytix Engineering | Technical Deep-Dive | Architecture · AI Security · Privacy Engineering
Tokenization vs. Encryption: Choosing the Right Data Protection Approach
Tokenization and encryption are both essential methods for protecting sensitive data and supporting regulatory compliance. While they appear in almost every major security framework, they work in fundamentally different ways. Selecting the wrong approach can lead to unnecessary architectural complexity or missed opportunities for compliance scope reduction.The choice between them depends on where your sensitive data resides, how it is accessed by identities (both human and non-human), and which specific risks you need to reduce to improve your data security posture.
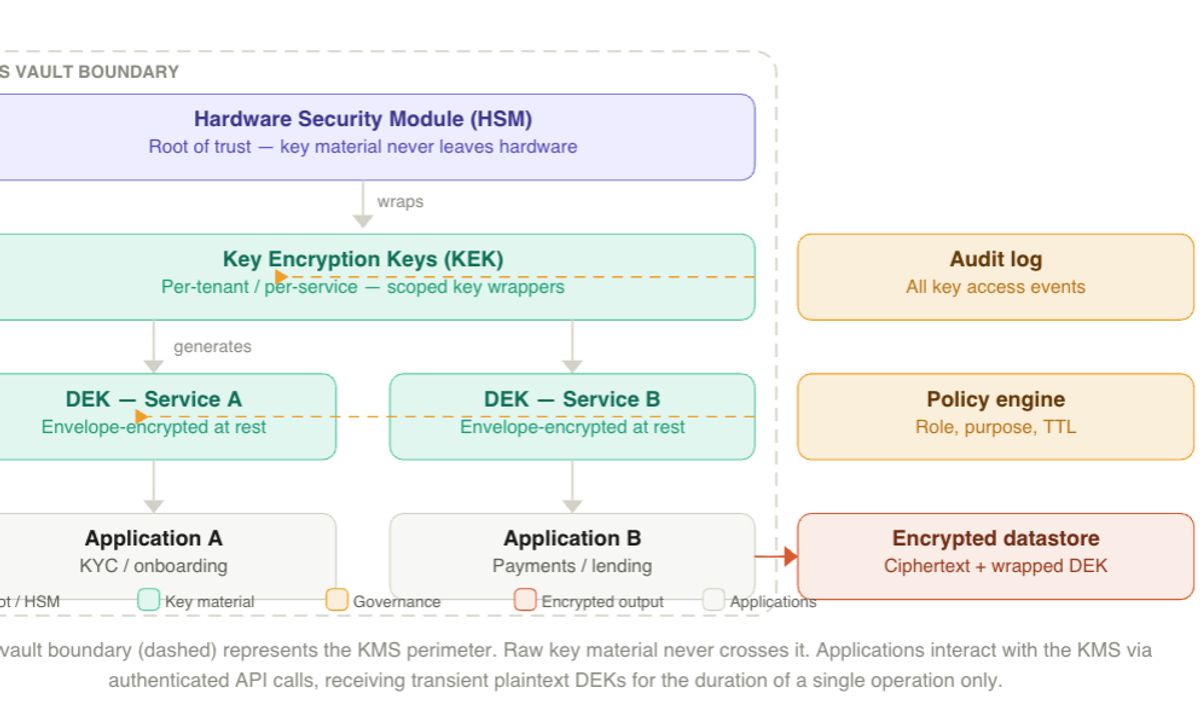
The Key to Everything: Why a Key Management System Is the Real Foundation of Your Encryption Strategy
Most enterprises encrypt their data. Almost none of them manage their encryption keys correctly. That gap is where breaches happen, and where a properly architected KMS closes them.
