Why the Frontend Is One of the Most Dangerous Places for PII And How to Fix It Architecturally
Securelytix Team
Product & Security
7 May 2026
Modern frontend applications handle sensitive user data across APIs, browser storage, analytics tools, and third-party scripts making the browser one of the largest yet least protected PII exposure surfaces. This article explores why frontend architectures leak sensitive data and how privacy-first design patterns like tokenization and secure data flow isolation help reduce risk.
The Invisible Risk at the Edge
There is a quiet assumption baked into most security architectures: that the real danger lives somewhere in the middle in databases, API servers, or cloud storage. The frontend, by contrast, is often treated as a thin display layer, a consumer of data rather than an originator of risk. In practice, this assumption is wrong, and in regulated industries like fintech, lending, or insurance, it can be catastrophically expensive to get wrong.
The frontend is where sensitive data is born. Before a PAN number reaches your tokenization service, before an Aadhaar number gets encrypted and stored, before a phone number is hashed, it passes through a browser. It lives, even if momentarily, in JavaScript memory. It travels across a network. It may be intercepted by a third-party analytics script you forgot was loaded on the page. This is the risk nobody draws on the architecture diagram.
At Securelytix, we spend a lot of time thinking about exactly this gap, the distance between where sensitive data first appears and where security controls are typically applied. This post is an attempt to think through that risk clearly: where it comes from, what makes the frontend uniquely exposed, and what a genuinely secure frontend architecture looks like in practice.
Where PII Actually Originates
Think about the typical onboarding journey for a fintech product. A user opens the app, lands on a KYC form, and begins entering their details: full name, date of birth, mobile number, PAN, and Aadhaar. They may also upload a scanned document. Each of these actions produces sensitive data in a place that is, by design, fully accessible to the user's browser environment.
That matters more than it sounds. The browser is not a controlled server room. It is a runtime that executes JavaScript from multiple sources, exposes its memory through developer tools, transmits data over networks that may be monitored, and logs information in ways that are easy to miss during development. Every field a user types into is, at some level, a security surface.
Forms are the most obvious entry point, but they are not the only one. Chatbot interfaces increasingly capture sensitive information through free-text inputs a user describing their situation might mention their Aadhaar number, their account balance, their outstanding loan amount. File uploads carry embedded metadata. Autofill behavior can cause browsers to populate fields that were never intended to hold personal data. The frontend is, in a very literal sense, the first place PII exists in your system, and it deserves to be treated accordingly.
This is a foundational premise behind how Securelytix approaches security design: the collection layer is not a passive conduit it is where the data lifecycle begins, and therefore where protection must begin.
Why the Browser Is a Hostile Environment
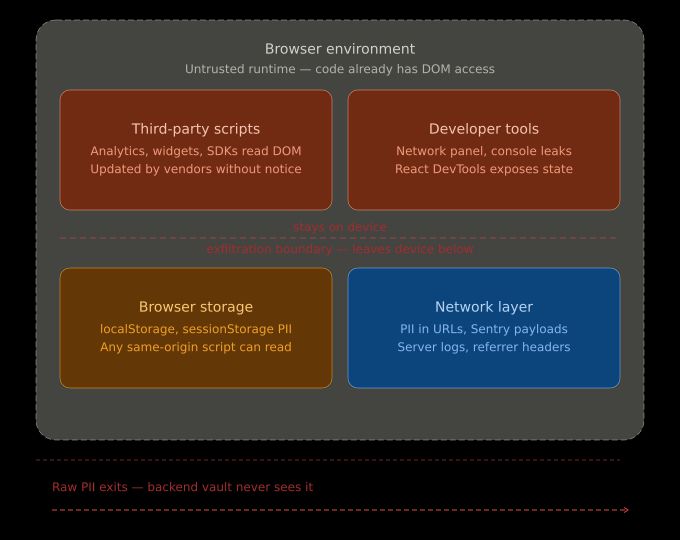
Backend engineers often think about threats in terms of network intrusion, SQL injection, or unauthorized API access. These are real threats, but they largely assume an attacker who is external to the system. The browser threat model is different. Many of the most serious risks in a frontend context come from code that is already running on the page, with legitimate access to the DOM.
Consider what a third-party JavaScript tag can do. An analytics library, a customer support widget, a performance monitoring SDK, any one of these may have access to the same DOM your application reads from. If a user types a PAN number into a form field, that value is readable by any script that can query the DOM. Most organizations have a dozen such scripts running on their pages, often loaded asynchronously and updated by vendors without prior notice.
Beyond third-party scripts, the browser's developer tools are a persistent concern. Network requests are visible in the Network panel. React's DevTools extension exposes component state. console.log statements left in by developers during debugging can emit sensitive values that persist in the browser's console history. None of these are exotic attack vectors they are default browser features that any user can access, and that can expose data to anyone with physical or remote access to a device.
There is also the question of browser storage. Data written to localStorage or sessionStorage persists beyond the lifecycle of a single page view. If your application caches a user's form progress, which is a perfectly reasonable UX decision, and that cache contains raw PII, you have created a durable copy of sensitive data in a location that any script on the same origin can read.
The network itself is another layer of exposure. Modern TLS protects most in-transit data, but it does not help when PII is accidentally included in URLs as query parameters, because those URLs appear in server logs, browser history, and referrer headers. It does not help when error monitoring tools like Sentry capture the full request payload and ship it to an external server. These are real mistakes, and they happen in production systems.
The Architectural Mistake: Treating the Backend as the Security Perimeter
Most security architectures are designed with the backend as the trust boundary. The thinking goes: data enters the system from untrusted sources, it is validated and sanitized at the API layer, sensitive fields are encrypted before storage, and access controls govern who can read what. This is sound thinking, and none of it should be abandoned.
The problem is the implicit corollary: if the backend handles security, the frontend does not need to. This produces systems where the API layer carefully tokenizes PAN numbers while the frontend is logging them to the console. It produces systems where PII is encrypted in the database while a third-party analytics tag reads it from the DOM. The backend perimeter is solid, but the data never safely reaches it.
This is not a hypothetical failure mode. It has played out in a number of real incidents. An organization implements rigorous data masking in its API responses, but a logging library captures the full request body before it is sent, shipping raw Aadhaar numbers to an external observability platform. Another organization carefully limits access to its user database, but a client-side error tracking tool captures unmasked form values when a validation error occurs. In both cases, the backend architecture is exactly as designed. The frontend architecture is where the breach happened.
The underlying issue is treating security as something that happens to data rather than something that protects it throughout its entire journey. Data does not become sensitive when it enters the database. It is sensitive the moment a user types it. This is the principle that drives Securelytix's approach: security must be built into the point of collection, not bolted on after the fact.
A Concrete Example: PAN/Aadhaar Onboarding in a Fintech App
To make this tangible, consider a lending application that collects PAN and Aadhaar as part of its KYC flow. Here is how data typically moves through such a system, and where things go wrong.
A user navigates to the KYC screen. The frontend renders a form with fields for PAN, Aadhaar, and a document upload. As the user types, React's controlled component state holds the PAN value in memory. An analytics script running on the page can, in principle, read from the DOM. If the developer console is open, any onChange logging will emit the value in real time.
When the user submits the form, the frontend constructs a JSON payload and sends it to a REST API endpoint. If the application uses a global request interceptor common in axios-based setups and that interceptor logs requests for debugging, the full payload, including the PAN number, is written to the console or, worse, to an external logging service.
On the network side, if someone has misconfigured the request and the PAN is passed as a query parameter rather than a body field, it will appear in server access logs, browser history, and any analytics platform that tracks URL patterns.
At the API layer, the backend receives the PAN, validates it, tokenizes it against a vault service, and stores only the token. The backend did everything right. But by this point, the raw PAN has potentially been logged in three separate places that the backend has no knowledge of and no control over.
This is the scenario Securelytix was designed to address not by replacing the backend vault, but by ensuring that sensitive data is handled with equivalent discipline at every point upstream of it.
What the Data Flow Actually Looks Like
Here is a simplified representation of the typical data flow in such a system, annotated with where exposure risks exist:
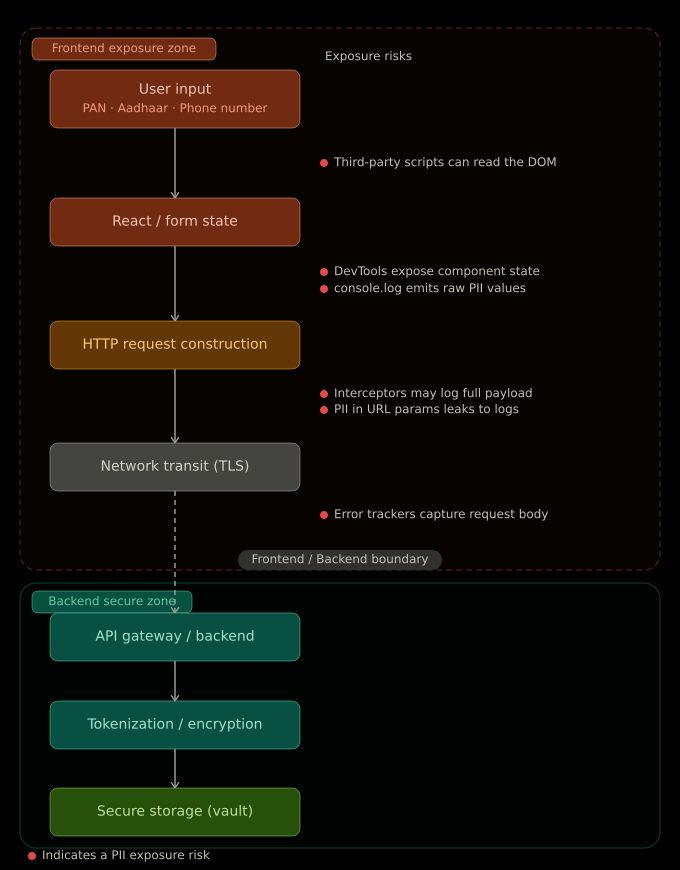
The backend architecture, represented by the downstream stages of this pipeline, is typically well-designed. The upstream stages where the user types, where JavaScript processes the input, where requests are constructed and dispatched, are where most real-world incidents occur, and they are the part that frontend engineers own.
Securelytix’s Approach to Frontend Security: Protecting PII at the Point of Collection
The answer is not to build a vault on the client side that would be both architecturally impossible and misguided. The answer is to treat the frontend as an active participant in the security posture of the system, not a passive conduit that just sends data along. This is precisely how Securelytix frames the problem: frontend security is not a set of patches on top of a backend-centric architecture; it is a discipline in its own right, applied at the layer where data first appears.

Controlling What Enters the DOM
The first discipline is to minimize how long raw PII lives in JavaScript memory. This means avoiding storing sensitive field values in global state management stores like Redux unless absolutely necessary. A PAN number that has been submitted does not need to remain in your application state. Once it has been sent to the API, it should be cleared. Controlled components should be preferred over uncontrolled ones precisely because you control when and how the value is accessed.
For document uploads, avoid reading the file contents into memory on the client side unless you need to. If the upload goes directly to a pre-signed URL, the frontend need never hold the binary data at all.
Eliminating Logging and Instrumentation Risks
Every logging statement in the codebase should be treated as a potential leak. A practical approach and one that Securelytix implements by default in its instrumentation layer is to build a logging abstraction that automatically redacts fields by name. Any object containing keys like pan, aadhaar, dob, or account_number is sanitized before the log is emitted. This is not foolproof, but it eliminates the most common accidental disclosures.
Third-party error tracking tools like Sentry support beforeSend hooks that allow you to scrub request payloads and stack trace arguments before they leave the browser. These hooks should be configured as a baseline, not an afterthought.
Hardening the Network Layer
Sensitive data should never appear in URLs. All PII must travel in request bodies over HTTPS, never as query parameters. API design should enforce this, and frontend code should be reviewed for any place where form data is serialized into a URL.
Request interceptors that exist for logging or debugging should be disabled in production builds through environment-based configuration, not by developer discipline alone. Discipline fails; build tooling does not.
Content Security Policy as a Hard Boundary
A well-configured Content Security Policy is one of the most effective tools available for limiting third-party script access to your application. A CSP that specifies a strict allowlist of trusted script sources prevents unauthorized or unexpectedly injected scripts from executing. Combined with Subresource Integrity checks on third-party scripts, this significantly reduces the risk that an analytics or tracking vendor's script update introduces a data exfiltration vector.
CSP headers should be set at the server or CDN level, not via meta tags in the HTML (meta tags can be modified by scripts loaded before them). The policy should be tested in report-only mode before enforcement, and reports should be monitored to catch violations early. At Securelytix, we treat CSP configuration as a first-class engineering artifact not a one-time setup, but an evolving boundary that is reviewed whenever new vendor integrations are introduced.
No Sensitive Data in Browser Storage
localStorage, sessionStorage, and IndexedDB should be treated as off-limits for any field that qualifies as PII. If your application needs to preserve form state across page refreshes for UX reasons a legitimate concern consider encrypting the stored data using a session-bound key that lives only in memory, or storing only non-sensitive progress indicators rather than field values.
Cookies that carry session tokens or authentication credentials should be set with HttpOnly and Secure flags, which prevents JavaScript from accessing them and ensures they are only transmitted over HTTPS.
The Evolving Role of Frontend Engineers in Security
Historically, security was something that happened around frontend engineers rather than to them. The security team reviewed backend code, audited API endpoints, and managed infrastructure. Frontend work was considered lower-risk because it did not directly touch the data store.
That boundary no longer holds. Modern frontend applications are large, complex systems that handle sensitive data, manage authentication flows, integrate with dozens of third-party services, and often run more logic than the backends they communicate with. The idea that a frontend engineer's primary job is to make things look right on the screen is a relic.
At the companies doing this well and in the work Securelytix does with product and engineering teams, frontend engineers are involved in threat modeling sessions. They make deliberate decisions about what goes into state, what gets logged, and what third-party scripts are permitted to execute. They write security-aware code review checklists. They champion CSP adoption even when it slows down the integration of a new vendor widget. This is not a niche skill it is becoming a baseline expectation.
The shift is also being driven by regulation. DPDP in India, GDPR in Europe, and similar frameworks globally are making organizations legally accountable for how PII is handled at every point in the data lifecycle, including collection. "The backend was secure" is not a sufficient defense if the breach happened at the form level.
Protecting Data at the Point of Collection
The deepest architectural insight in this space is also the simplest: data is most vulnerable at the moment it enters your system, not after it has been processed and stored. Encryption at rest and access controls on databases protect data that has already survived its most dangerous journey the one from a user's keyboard to your API.\
A genuinely secure architecture does not treat the frontend as a trusted internal system that happens to face the user. It treats the browser as an untrusted environment, limits what sensitive data is held there and for how long, imposes hard boundaries on what scripts can execute, and instruments the pipeline to detect accidental exposure before it becomes a breach. This is the philosophy Securelytix is built on: security at the point of collection, applied systematically and verifiably, not as a checklist item but as a continuous engineering discipline.
The vault-first mentality build a secure backend and trust that data will reach it safely is not wrong so much as incomplete. It solves the second half of the problem and ignores the first. Defense in depth means protecting data at every layer it passes through, starting with the layer where it first appears: the frontend, in the browser, in the hands of a user who just typed something sensitive and hit submit.
That moment is where security either holds or fails. Designing for it is not optional.
Ready to Secure Sensitive Data?
Explore how Securelytix helps teams protect sensitive data, enforce privacy controls, and build secure AI-ready infrastructure.
