The Key to Everything: Why a Key Management System Is the Real Foundation of Your Encryption Strategy
Securelytix Team
Product & Security
6 May 2026
Most enterprises encrypt their data. Almost none of them manage their encryption keys correctly. That gap is where breaches happen, and where a properly architected KMS closes them.
The Encryption Illusion
Encryption is not a security outcome. It is a security mechanism. The outcome depends entirely on what you do with the keys. An organisation that encrypts its customer data at rest but stores the encryption keys in the same database, in the same environment, managed by the same access policies, has not achieved meaningful protection. It has achieved the appearance of protection, which is considerably more dangerous, because it produces confidence that has not been earned.
Encrypting data without properly managing the keys is the equivalent of locking your vault and leaving the key in the door. The lock is real. The protection is not.
"Encrypting data without properly managing the keys is the equivalent of locking your vault and leaving the key in the door. The lock is real. The protection is not."
What a Key Management System Actually Does
A Key Management System (KMS) is the infrastructure that governs the full lifecycle of cryptographic keys — their generation, storage, distribution, rotation, revocation, and destruction. It is not simply a secure place to store keys, though secure storage is part of it. A KMS enforces policy on who can access which keys, for what purpose, at what time, and with what level of authority. It produces an immutable audit trail of every key operation. And it ensures that the keys themselves, at their root, never exist in plaintext outside of a hardware boundary.
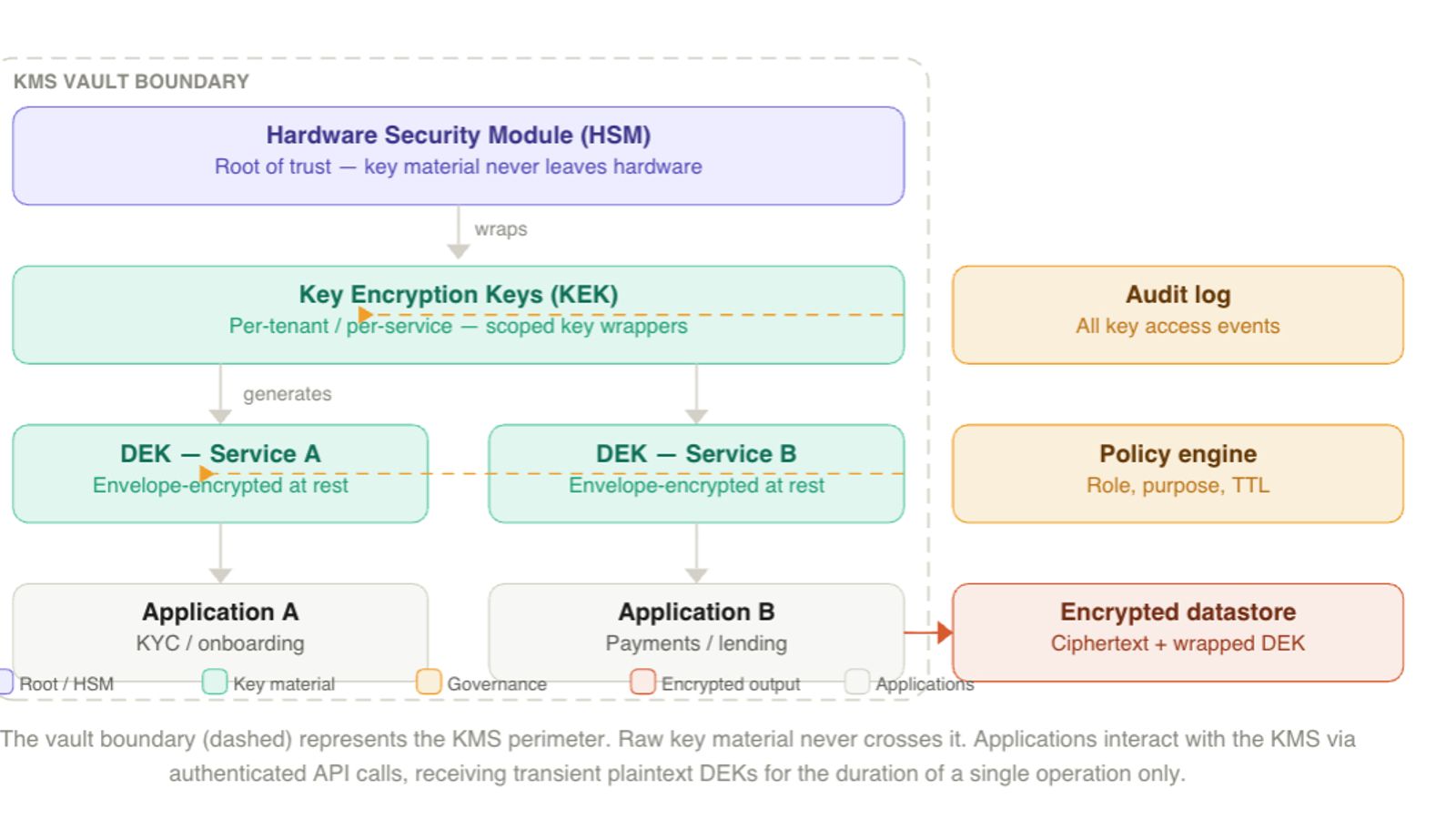
This architecture relies on a hierarchical key management model anchored by a hardware-backed root of trust, typically an HSM, which securely generates and protects master keys without ever exposing them. Beneath this root are Key Encryption Keys (KEKs), scoped to tenants or services, which are used to encrypt short-lived Data Encryption Keys (DEKs). Each DEK is generated per encryption operation, used immediately, and stored only in encrypted (wrapped) form. During decryption, authenticated services temporarily access the plaintext DEK within a secure boundary, ensuring it never persists outside the system. This approach known as envelope encryption ensures that even if encrypted data and wrapped keys are exposed, they remain unusable without access to higher levels of the key hierarchy, maintaining a strong, physically anchored chain of trust.
Where Enterprises Get This Wrong
The failure patterns are consistent enough that they can be enumerated. They are not failures of intent, every engineering team intends to manage keys properly. They are failures of architecture, accumulated over years of pragmatic shortcuts.
Flat key model (single key for everything) One encryption key is used across all data, making rotation extremely difficult → in practice, keys never get rotated.
Keys stored with the data If attackers access the database, they often get both encrypted data and keys → encryption becomes useless.
No audit trail for key access No logs of who accessed keys or when → impossible to investigate breaches or ensure accountability.
BYOK without proper KMS Organizations bring their own keys but lack proper management infrastructure → compliance is met, but real security control is missing.
The Regulatory Imperative: DPDP, RBI, and GDPR
- Key management = compliance requirement Not optional—mandatory for regulated organisations.
- DPDP Act (India) Requires “reasonable security safeguards,” which include proper key management aligned with standards like ISO 27001.
- Audit expectation Encryption without control over keys is not enough to prove compliance.
- RBI guidelines Mandate strict controls over key lifecycle:
- Storage
- Access
- Rotation
- Audit trails
- GDPR (EU exposure) Encryption is valid only if:
- Keys are securely managed
- Proper access controls exist
- Key-data separation is maintained
- Core takeaway Encryption alone ≠ security. Controlled, auditable key management is what regulators actually require.
What a Production KMS Architecture Looks Like
A production KMS architecture for a financial services organisation handling Aadhaar-linked data, PAN records, and banking credentials would implement the following controls as baseline, not as aspirational targets.
Per-tenant, per-purpose key hierarchy:-
KEKs (Key Encryption Keys) are created separately for different types of data like KYC, transactions, or accounts—not because encryption needs it, but to control access. This way, a person who is allowed to work on transaction data cannot access sensitive KYC data. The key hierarchy ensures this separation automatically, improving security and access control.
Automated key rotation with zero downtime:-
Data Encryption Keys (DEKs) are used once and then stored in an encrypted (wrapped) form. When it’s time to rotate keys, the system doesn’t need to re-encrypt all the data again. Instead, it simply re-encrypts (re-wraps) the DEKs using a new Key Encryption Key (KEK), while the actual data stays unchanged. This makes key rotation fast and efficient. Because of envelope encryption, rotation is just a small key update process—not a heavy data migration—and it can be automated by policies instead of relying on manual effort.
Cryptographic audit trail (easy explanation):-
Every time the KMS does anything with a key—like creating, using, rotating, or deleting it—it records a detailed log. This log includes who made the request, which key was used, what action was performed, when it happened, and whether it succeeded. These logs cannot be changed or deleted, so they act like a secure history book. If something goes wrong or an audit happens, you can clearly see who accessed what and when.
Policy engine with purpose limitation (easy explanation):-
Access to keys is not just about “who you are,” but also “why you are accessing it.” The system checks both your identity and your purpose before allowing access. For example, if a service is allowed to decrypt data for fraud checks, it cannot use the same data for marketing. This ensures data is only used for the right reason, helping meet privacy rules like DPDP and GDPR.
The Operational Reality: KMS and the DevSecOps Pipeline
"The key never lives in an environment variable. It never appears in a deployment log. The isolation is cryptographic — and cryptographic isolation cannot be defeated by operational convenience."
The Architecture That Holds
Think about it this way. A bank vault door is useless if you leave the key in the lock. The door is real. The security is not. The same logic applies to encryption. Most of the enterprises that suffered serious data breaches in recent years did not lack encryption — they lacked control over their encryption keys. The data was locked. The key was sitting in a config file, copied across three environments, accessible to anyone who had ever touched the codebase.
"The data was encrypted. The keys were not managed. And when an attacker found the keys, the encryption provided no protection at all — because it had no foundation."
What a KMS actually gives you:-
A Key Management System does not add another lock. It makes every existing lock meaningful by ensuring the keys to those locks are genuinely controlled — not just stored somewhere that feels secure.
- Your database encryption is only meaningful if the key used to encrypt it is properly managed. A KMS ensures that.
- Your backup encryption is only meaningful if the key is rotated and audited. A KMS automates that.
- Your tokenisation is only meaningful if the key that maps tokens to real values is governed as carefully as the data itself. A KMS enforces that.
Frequently Asked Questions
What is a Key Management System (KMS) and why does it matter for data security?
A Key Management System (KMS) is infrastructure that governs the complete lifecycle of cryptographic keys- generation, storage, distribution, rotation, revocation, and destruction. It matters because encryption without key management is security theatre: if the encryption keys are poorly managed, accessible to unauthorised parties, or stored alongside the data they protect, the encryption provides no real protection. A KMS enforces policy-based access controls, maintains cryptographic audit trails, and ensures that master key material never exists in plaintext outside a hardware boundary such as an HSM.
What is envelope encryption and how does a KMS use it?
Envelope encryption is the pattern where a unique Data Encryption Key (DEK) is generated per record or per operation, used to encrypt the data, and then itself encrypted (wrapped) by a Key Encryption Key (KEK) that is held inside the KMS. The encrypted data and the wrapped DEK can be stored together — they are useless without the KEK. To decrypt, the application presents itself to the KMS, which unwraps the DEK inside its own boundary and returns it briefly in plaintext for the decryption operation. This means key rotation does not require re-encrypting all data — only the DEK needs to be re-wrapped under a new KEK, leaving the underlying ciphertext unchanged.
Is a KMS required for compliance with the DPDP Act 2023 in India?
The DPDP Act 2023 requires Data Fiduciaries to implement reasonable security safeguards to prevent personal data breaches. While the Act does not prescribe specific technical controls by name, the expected DPDP Rules reference IS/ISO/IEC 27001 compliance — a standard that explicitly requires documented cryptographic key management controls. For regulated financial entities, the RBI's Master Direction on IT Framework and cyber security circulars go further, requiring documented key lifecycle management, access restrictions, and audit trails. Organisations that encrypt personal data without proper key management will find it difficult to evidence compliance under either framework.
What is BYOK (Bring Your Own Key) and when should an organisation use it?
BYOK (Bring Your Own Key) is an arrangement where an organisation generates and controls their own root key material, which is then supplied to a cloud provider to use for encrypting data in that cloud environment. It is increasingly required by regulators — including under RBI's data localisation guidance and the DPDP Act's requirements for sensitive personal data — because it ensures that the cloud provider cannot access plaintext data without the organisation's key, which is under the organisation's control. However, BYOK is only meaningful if the organisation has a proper KMS to manage the key they are bringing. BYOK without KMS infrastructure simply shifts an unmanaged key from one location to another without adding governance.
What is a Hardware Security Module (HSM) and why is it required in a KMS?
A Hardware Security Module (HSM) is a tamper-resistant physical device designed to generate, store, and perform cryptographic operations using key material that never leaves the hardware boundary in plaintext. HSMs certified to FIPS 140-2 Level 3 or higher are physically designed to detect and resist tampering — attempts to extract key material physically destroy the device. In a KMS, the HSM serves as the Root of Trust: the apex of the key hierarchy from which all other keys derive their authority. Using an HSM ensures that even if an attacker gains complete access to the software layer of the system, the root cryptographic material cannot be extracted because it is anchored in hardware that physically prevents it.
How often should encryption keys be rotated, and how does a KMS make rotation operationally feasible?
Key rotation frequency depends on the key type and the sensitivity of the data. Data Encryption Keys (DEKs) in an envelope encryption model are effectively single-use — a new DEK is generated per operation — so they rotate automatically. Key Encryption Keys (KEKs) are typically rotated annually or following any security event, personnel change, or suspected compromise. Without a KMS, rotation is operationally painful because it requires re-encrypting every record protected by the old key. With a properly implemented KMS using envelope encryption, rotation of a KEK requires only re-wrapping the stored DEKs under the new KEK — the underlying ciphertext is untouched. This makes rotation a routine, automated operation rather than an emergency data migration project.
What is the difference between a KMS and a secrets manager?
A secrets manager (such as HashiCorp Vault's secret storage, AWS Secrets Manager, or Azure Key Vault's secret mode) stores arbitrary secret values — API keys, database passwords, certificates, connection strings — and controls access to them. A KMS is specifically designed for cryptographic key material and performs cryptographic operations on behalf of callers rather than simply handing out key values. The critical distinction is that a proper KMS with HSM backing never returns the raw key material to the caller — it performs the encrypt or decrypt operation internally and returns only the result. A secrets manager typically returns the secret value to the authorised caller, who then uses it locally. For protecting personal data under Indian and international privacy law, a KMS provides structurally stronger guarantees than a secrets manager used alone.
Ready to Secure Sensitive Data?
Explore how Securelytix helps teams protect sensitive data, enforce privacy controls, and build secure AI-ready infrastructure.
